[ ENCRYPTED COMMUNICATIONS DEVICE ]
Your Phone Knows
Everything
About You.
The Question Is... Who Else Does?
Your smartphone isn't just a device—it's a tracking system,
communication hub, and access point to your entire business.
[ THREAT ANALYSIS ]
Your Phone Is Big Tech's
Favorite Surveillance Tool
Your phone tracks
where you go
Logs who you
communicate with
This is a Paragraph Font
Builds a profile
of your behavior
Shares data across apps,
platforms, and networks
"Your phone is a tracking beacon broadcasting your entire life."
— PRIVACELL
If Someone Compromise Your Phone...
They may gain access to:

Business email

Financial apps

Password resets

Client conversations

Internal systems
[ CRITICAL ]
Your phone isn't just a device. It's a gateway to your entire business.
Introducing
HackProof Phone
Take Back Control of Your Data. Your Device. Your Privacy.

Control over their data
Full ownership of every byte

Reduced exposure to tracking
Invisible to surveillance

Stronger mobile security
Hardware-level protection

A device that works for them
Not against them
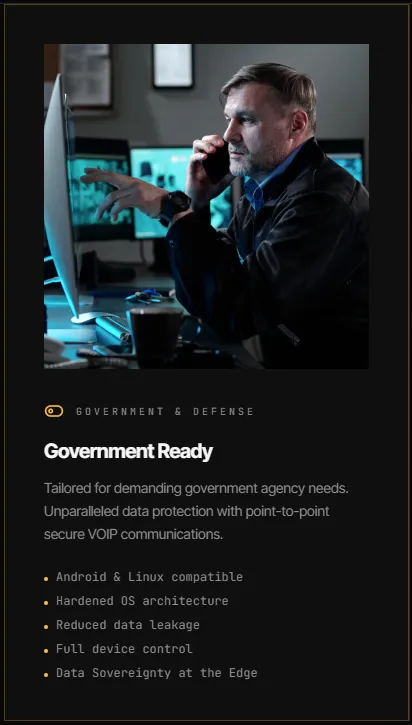
[ TECHNOLOGY STACK ]
Powered by
XTC Mobile
Secure Mobility Platform for Business, Government & Military.
FOUNDED BY CYBERSECURITY ADVISOR SERGEY POLTEV
AUTHORIZED RESELLER — OTTAWA, CANADA

[ HACKPROOFPHONE x XTC MOBILE ]
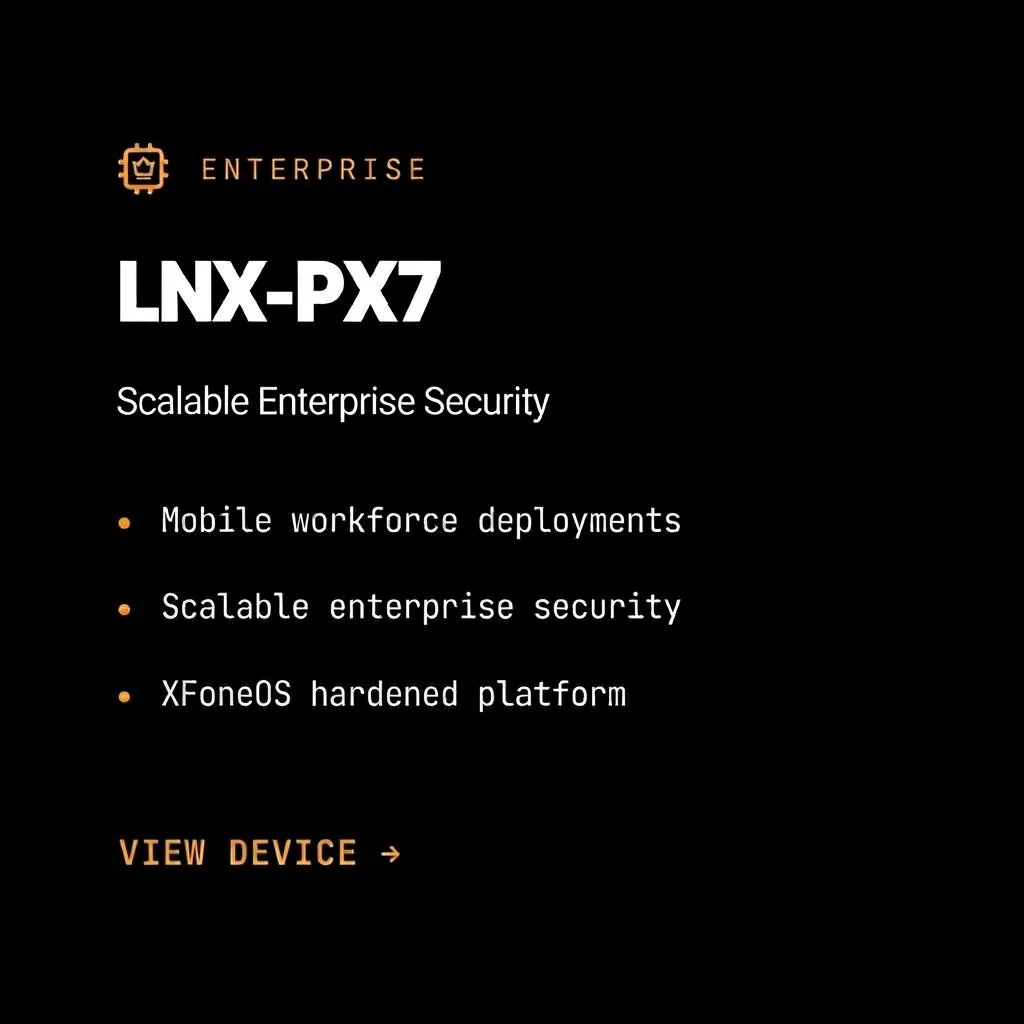
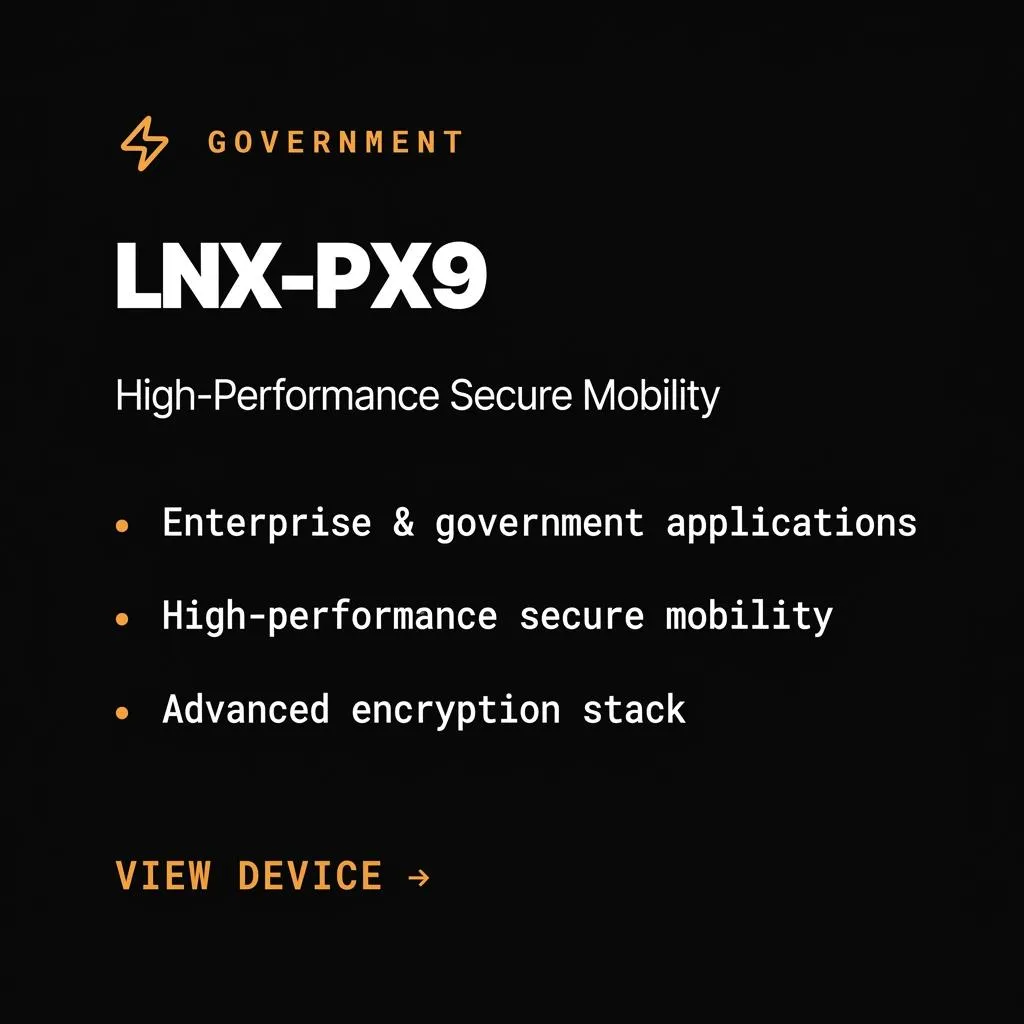
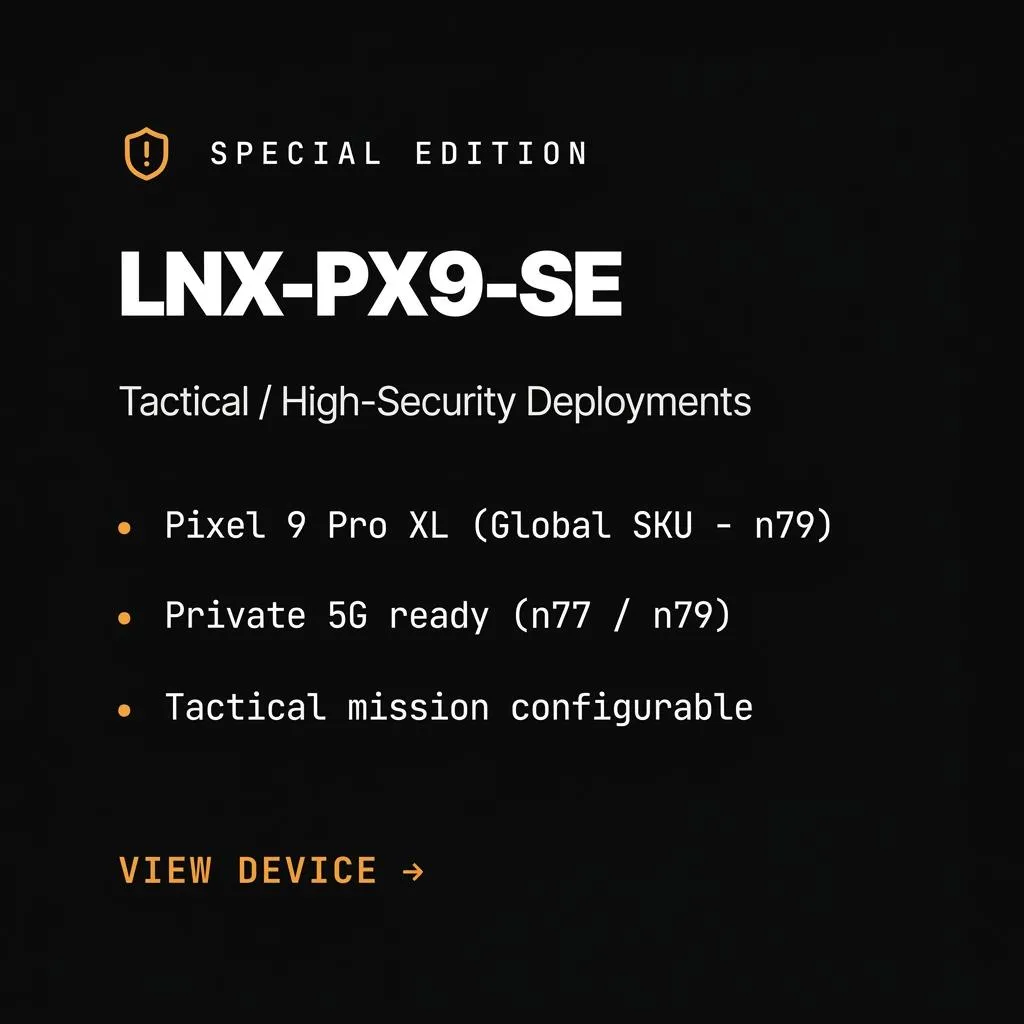
FULL PRODUCT LINEUP - LYNX PHONE
[ STILL NOT SURE ]
Frequently Asked Questions
Question 1: Is Hackproof Phone truly "hackproof"?
HackProof Phone is designed to significantly improve privacy and reduce cybersecurity risk. No device can be guaranteed to be completely 'hack proof.' Security depends on proper configuration, usage, and overall cybersecurity practices.
Question 2: Who is this phone designed for?
Business owners, executives, and professionals who want control over their data, communications, and risk exposure. This is not about hiding—it's about taking control.
Question 3: What technology powers the Hackproof Phone?
HackProof Phone is powered by secure mobile technology from XTC Mobile, featuring OS-level security, user-controlled permissions, and privacy-first architecture.
Question 4: Can I still use regular apps?
Yes, but with full control over what data each app can access. You decide what permissions to grant and can revoke them at any time.
Question 5: How do I get started?
Request your HackProof Phone or book a 15-minute consultation to discuss your specific security needs and how HackProof can help protect your business.
[ CONTROLLED ACCESS - SPECIAL ORDER ONLY ]
Start With Your Phone. Secure the Business.
Privacy . Security . Control .
Limited production allocation. Deployment aligned to mission requirements. Direct engagement with qualified organizations.

Cybersecurity authority and author of Hack Proof: A Guide to Cybersecurity for Your Business
Join our Mailing List
And that's just a peek at what we offer. Get more marketing tips straight to your inbox.
© 2025 . All rights reserved.
© 2025 . All rights reserved.
Cookie Policy
Terms of Use
Privacy Policy